Official PCI Security Standards Council Site - Verify PCI Compliance, Download Data Security and Credit Card Security Standards
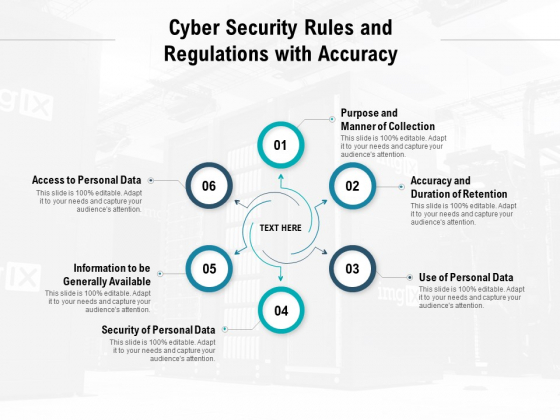
Cyber Security Rules And Regulations With Accuracy Ppt PowerPoint Presentation Slides Outfit - PowerPoint Templates

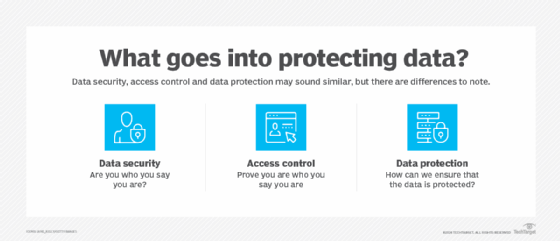
Devoteam on Twitter: "Data #protection and #security is key to every business. Know the best #practices to secure your #information network and #people. Find what could be improved in your company by